

Updated January 3, 2025
Effectively securing a company through employees requires that companies accept a shift in security paradigm, one which focuses on a system of distributed trust and end-to-end encryption.
Companies create cybersecurity policies in the hopes of improving their company’s security profile.
By establishing protocols for the use of personal devices, passwords, and password updates, executives create policies they hope will effectively protect their companies.
Looking for a IT Services agency?
Compare our list of top IT Services companies near you
The thinking here is that if policies are created and clearly communicated, employees will follow them.
But, as recently reported by Clutch, “being subject to a company’s cybersecurity policy does not guarantee that employees follow it.”
Instead, traditional approaches to improving security get in the way of business and, as a result, get bypassed.
To solve this issue, CISOs need to create a security policy that gets out of employees’ ways and becomes a seamless addition to their workflows.
This article argues that the best approach to cybersecurity is to make it easy for employees to do their work securely, as opposed to foisting more and more complicated policies upon them, by using end-to-end encryption.
The problem with traditional approaches to security is that they interrupt business workflows.
Passwords, for example, are considered the primary form of cybersecurity for most employees. Yet, most employees’ approach to password protection is to only change a character or two in their password from one month to the next.
Only a minority implement more complex forms of password protection such as different passwords for each account or two-factor authentication (2FA).
The reason employees don’t opt for more secure passwords and protection schemes is that these methods become challenging to implement and maintain.
When employees encounter a perceived tradeoff between getting their job done and following a prescribed security practice, the overwhelming majority simply find a way to bypass the security policy in order to do their jobs.
This reality shouldn’t surprise us. It’s important to recognize that for employees, both following security training and getting your job done in a dynamic technology environment is incredibly difficult.
As a result, sensitive intellectual property, personally identifiable information, and other highly confidential information ultimately end up floating around in documents and emails on insecure channels.
Additionally, with all the focus on password updates and authentication, employees lose sight of the fact that “normal” communications and document sharing can also be incredibly vulnerable endpoints that cybercriminals can use to access entire company systems.
Most employees believe that important information somehow looks different than regular communications. However, this is not the case, since most of an organization's intellectual capital is actually found in everyday documents.
Today’s security paradigm focuses significantly on protecting centrally-stored data. This basically entails employers running a race against cyberintruders by building ever-taller walls or more complex password policies in hopes of keeping intruders out.
Employers hope these walls will protect their important assets such as emails and files. However, these walls can never be built tall enough to be truly effective.
Taller IT walls do not work. We need to accept is that no matter how high we try to build the walls, criminals will always find a way to scale them and access the cloud.
Thus, it’s time for a new security paradigm, one that assumes that company systems will be attacked and passwords will be stolen.
Assuming this as a given allows companies to save valuable time and money and avoid unneeded frustration. It also allows us to focus on encrypting data so that even if data is stolen, it cannot be used.
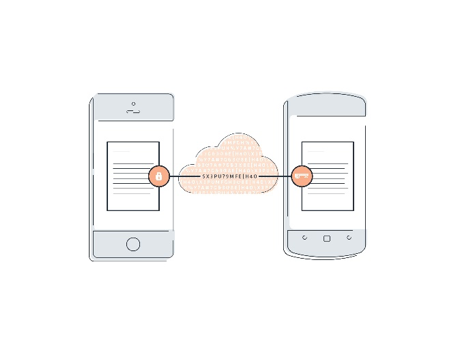
With end-to-end encryption, only the message recipient can ever decrypt the data.
An important component of the end-to-end paradigm shift is ensuring that there is no central point of trust, or a singular super-user or admin who has unfettered access to corporate data.
Preventing sole ownership means that there is no way for attackers to steal the key from the super-user or admin and have access to all corporate assets.
A smarter approach is to adopt a system of "distributed trust," in which you spread out trust among multiple reliable approval groups. With approval groups, a company can require a certain number of people to agree before a privileged activity can occur, such as granting access to a new user.
With this shift in thinking, we can stop focusing on constant password updates and instead focus on how to limit the attack surface that an attacker can access.
This philosophy of data and email management lies behind the development of our secure email and drive manager, which operates using the paradigm that servers and email will be attacked.
In the PreVeil model, emails and files are encrypted with keys that are only accessible to recipients of the data. These recipients are the only ones with the required decryption keys, which they store on their phones and computers. There’s no password for an attacker to steal that provides access to data. Since an attacker doesn’t possess a user’s device, they don’t’ have the required keys to decrypt data intended for that user.
While this concept of encryption might seem complicated, the implementation is quite easy. PreVeil’s encryption software lives seamlessly in the office environment and works on top of existing office tools. This makes security easy to use and part of the general workflow.
Employees want to do the right thing. However, their actions often make them the victim of schemes which compromise their passwords or files.
Establishing a system of distributed trust means you never have to worry about one user or one administrator as the single point of compromise for files, and not relying on passwords means that there are no proverbial keys to the kingdom that can be stolen.
Even if one user is compromised, the whole basket of apples is not overturned. In essence, the attack surface decreases and everyone’s data is more secure.
If employers want security to be used by the vast majority of users, they have to make it easy to use. Security needs to be easy, get out of employees’ ways, and be a seamless addition to workflows. In fact, it should be so easy that users don’t even recognize they are using it.


