![How to Create a Budget for BI & Analytics Services [With Template]](https://img.shgstatic.com/clutch-static-prod/image/resize/715x400/s3fs-public/article/f07e9d6bd89e7f70df9c94301acdd847.png)
![How to Create a Budget for BI & Analytics Services [With Template]](https://img.shgstatic.com/clutch-static-prod/image/resize/715x400/s3fs-public/article/f07e9d6bd89e7f70df9c94301acdd847.png)
Updated May 7, 2025
Cybersecurity is an essential investment for every business in the modern world. Without a reliable solution in place, you risk your sensitive data from malicious cybercriminals. However, finding a dependable partner to help protect your digital assets isn’t a simple ordeal. With all the choices available, it’s hard to identify which agency best suits your needs. Here’s our in-depth checklist to help you choose and hire the right cybersecurity firm.
Cybersecurity is the act of protecting digital assets and eliminating all kinds of vulnerabilities. Now more than ever, confidential information, customer data, and personal data are all at risk from malicious cybercriminals. The number of cyberattacks has dramatically increased over recent years, costing businesses millions of dollars in lawsuits and data loss.
Essentially, cybersecurity companies are a type of IT service provider that primarily specializes in helping companies avoid headache-inducing lawsuits by securing their sensitive data and protecting their online operations. These firms offer extensive services like proactive network security, penetration testing, and cybersecurity training.
Looking for a IT Services agency?
Compare our list of top IT Services companies near you
Hiring a dedicated cybersecurity firm brings a plethora of benefits including reduced downtime, risk mitigation, and protection from hackers. Their work is critical to ensuring companies maintain continuity for their operations by avoiding various cybersecurity threats.
Searching and matching with the right cybersecurity partner can be challenging, especially since there are plenty of firms vying for your project. In this checklist, we’ll go through everything you need to take into consideration when hiring a cybersecurity firm.
How to Choose a Cybersecurity Firm
The first and arguably the most important step when hiring any service provider is to define your goals. Before you go on and scour the internet for a top partner, you need to have a clear understanding of your business needs and goals.
The common reasons why businesses hire cybersecurity firms are:
SMART objectives — specific, measurable, achievable, relevant, and time-bound — can help business owners remain motivated and focused.
Regardless of how long, big, and challenging the partnership will be, transparent objectives will help you create a set of criteria when hiring a partner, preparing a budget, and determining what type of security measures you need.
Once you’ve successfully defined your goals, you can proceed to prepare a dedicated budget for your project. Since you already have all the key information you need, setting a practical budget based on research is much easier.
Creating a budget is important to understanding financial limitations and seeing if your partnership brings in the right return on investment (ROI). It will also help you when you’re searching for service providers as you can quickly filter them by the average cost of their projects.
When setting a comprehensive budget, it’s important to consult with your leadership team and do your research. You should also consider how long the budget will last, fixed costs, variable costs, and even cash flow.
Remember, your budget is your project’s financial roadmap to success, especially for small businesses with limited resources. It’s also your responsibility to prepare backup measures in case you go beyond or encounter unexpected costs.
Know all the factors you need to consider here: “How to Create a Cybersecurity Budget [with Template]”
As emphasized, there are tons of cybersecurity firms out there, and it can be an intimidating task to find the right partner for your project. After you’ve accomplished the first two steps, the research phase shouldn’t be too complicated.
Since the cybersecurity industry is broad, it’s common for service providers to have their own expertise. For instance, you can search for firms proficient in phishing attacks, malware, or ransomware attacks.
During this stage, being organized can help you a lot. You can create a list of criteria when searching for reliable partners. Here are a few variables you should consider when looking for the ideal firm:
In addition to these, make sure you also consider their soft skills, like responsiveness and compassion, when researching potential service providers.
It would be impossible to reach out and consult with every firm you see fit for your project. Thus, creating a shortlist of only the top firms to interview is essential.
To efficiently filter the choices, you can take your time reading more about each firm’s profiles, case studies, and client reviews.
Clutch is a third-party review platform that collects and publishes in-depth client ratings to help browsers make an informed decision. These ratings help take a deep dive into the project management, communication skills, and approach of each firm. Evaluating client reviews is a great way to see if a service provider delivers on their promises and has recurring issues.
Additionally, Clutch lets you efficiently filter firms based on their location, average rating, and price. You just need to align these with your requirements and you won’t have to worry about wasting time consulting with firms that don’t match your goals.
Shortlists should only have around four to five options. Putting ten firms on a “shortlist” defeats its purpose.
Basing your final decision based on what you’ve read is not a wise decision. Before you officially hire any service provider, it’s important to conduct thorough interviews to get deeper insights about them. If done correctly, interviews will let you gather all the helpful information you need and also give them a chance to make a great first impression.
Reach out to the firms you’ve included in your shortlist to schedule an interview and ask for a Request For Proposal (RFP), a document that solicits a bid for their services. Once you’ve confirmed a schedule with them and received the RFP, you can go ahead and prepare key questions to help your decision-making process.
Here are some questions you can ask:
Remember, don’t hesitate to ask everything you need to know about their services during the interview and give them the chance to clarify whatever concerns you have.
Read more here: “B2B Partnerships: Questions to Ask Potential Business Partners”
After conducting the interviews, it’s time to narrow down the options. Ideally, the choice should go down to two after you’ve gathered all the necessary information.
Call on your leadership team and discuss all the pros and cons of each option. Having the suggestions and thoughts of other people within your organization can help you make a wiser decision. They may have different insights or perspectives that can be invaluable when choosing the right firm.
In some cases, you may end up interviewing great companies but they don’t exactly meet all of the criteria you’ve set. For this, you can review your priorities to determine which best meets your main requirements.
Of course, it’s a big investment so you should consider every factor including their company culture before hiring them.
When you’ve finally come up with a decision, the last step is to hire and onboard your chosen cybersecurity partner. Reach out once again to let them know about your verdict and request a service level agreement (SLA).
For context, SLAs are legal documents or contracts that detail the scope of service and relationship between a firm and a client. It should contain the terms, operating conditions, payment obligations, and even renewal provisions.
Before you sign the SLA, make sure you once again sit down with your team to read and scrutinize the document to avoid unfair risks. These contracts will legally bind both parties’ commitments so it’s essential you do a thorough assessment before penning your signature.
To sum it all up, refer to this checklist when searching for the right partner for your needs.
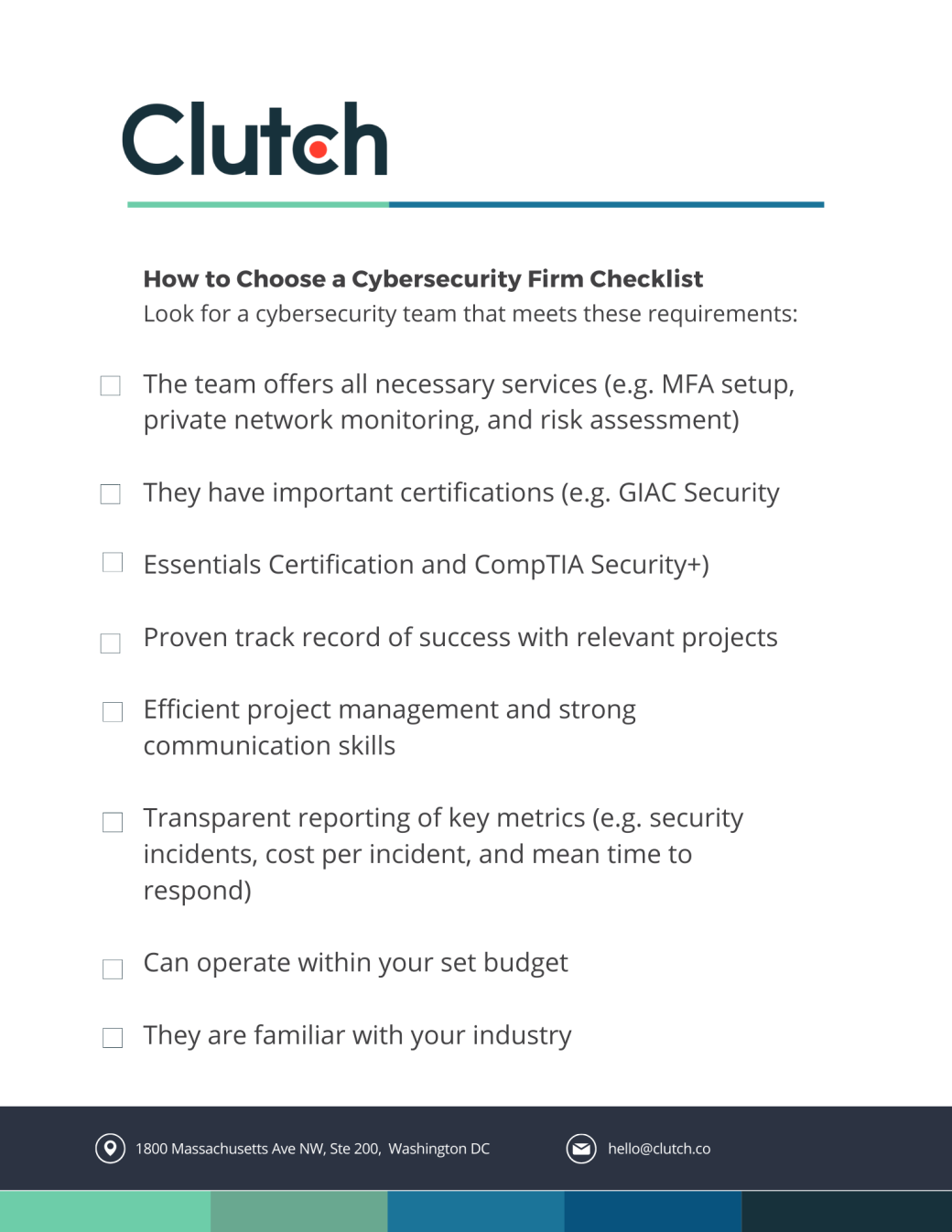
Download this checklist before hiring a cybersecurity firm.
Company data should be protected at all costs. Nowadays, strong passwords, commercial antivirus software, and VPNs won’t cut it because hackers are just constantly getting better at what they do.
Investing in cutting-edge cybersecurity should be a priority for every organization, especially considering the many regulations and data privacy laws in place.
The right cybersecurity firm will not just protect your assets but also give you the peace of mind you deserve. At the end of the day, they’re the keys to safeguarding your business from fraud, viruses, and varying security attacks.
Work with a company that can protect you like a state-of-the-art firewall. Find and connect with the leading cybersecurity service providers on Clutch.
![How to Create a Budget for BI & Analytics Services [With Template]](https://img.shgstatic.com/clutch-static-prod/image/resize/715x400/s3fs-public/article/f07e9d6bd89e7f70df9c94301acdd847.png)

