Updated March 5, 2026
Cyberattacks on APIs have surged over the last year, impacting businesses around the world. Protect your business by following these API best practices.
We all have booked flights or ordered something online, but we are unaware of how our requests get fulfilled. A secret facility, known as the API, works behind the scenes. Whether extracting the best flights or processing e-commerce orders, an Application Processing Interface is the unsung hero.
Recently, APIs have surged significantly thanks to their scalability, integration, and automation benefits. That has also led to a surge in API management. According to current market stats, the market for API management will be USD 32.31 billion by 2031, a growth of 24.80%. Considering these numbers, it is the stage for now and the future.
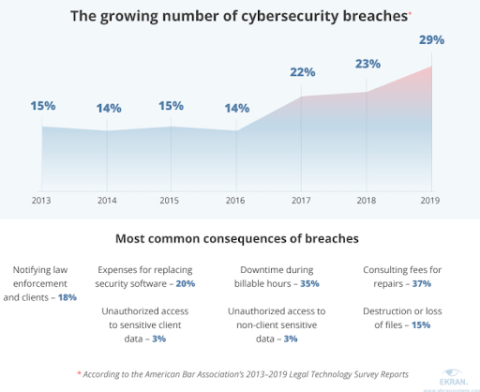
On the contrary, the surge in API use has also lured malicious actors into the picture. Cyberattacks on APIs surged by 20% in 2024 compared to 2023. These attacks have affected 1 in every 4.6 organizations worldwide. Hence, there is a need for robust API security practices.
Looking for a cybersecurity company? Search industry-leading service providers on Clutch. Filter based on client ratings, pricing, and location to find the perfect partner for your porject.
APIs are responsible for transferring data across networks and devices. In some cases, sensitive data is involved, and this is where it gets critical. Malicious actors employ attacks like DDoS, Man-in-the-middle, SQL injection, etc., to access this data.
API security is a term used to define methods, tips, and processes to strengthen API security. These methods fix underlying security vulnerabilities to ensure robust data protection. Rather than using traditional password-based systems, it includes the use of:
API security means using features to ensure that data is kept safe, private, and available by detecting and stopping unauthorized access.
APIs look like a bridge between different systems. Attackers find them attractive because they can use them to access a system. Web developers usually trust APIs, but sometimes, they need to remember to secure them. API security keeps your application and user data safe from unauthorized access, data breaches, and cyber-attacks.
Let’s have a look at more benefits of using API security:
When a user operates an online website for some task, let's say, ticket booking, they enter their essential information. Proper API security measures can ensure secure communication between the user and the server. Critical methods like data encryption and secure logins ensure sensitive data security while in transit. Many businesses combine API integration with VoIP to increase the functionality and effectiveness of business communication systems.
A suitable example to understand the need for API security is the Clubhouse leak of 2021. The Clubhouse API suffered a breach that led to a data leak of 1.3 million users. This was a need for pre-need authentication methods involving authentication tokens or passwords.
Why do a maximum number of people buy online from Amazon? Business authority and standards. Every business must maintain some standards to function effectively in the marketplace. Companies can establish users' trust in handling their data by implementing API security measures.
An organization may have a lot of critical information on its servers. Anyone who breaches them could leverage the data to commit cybercrimes, sometimes affecting the entire organizational network. Therefore, API security is necessary to find threats in third-party applications and keep malicious actors at bay.
A similar attack on the Microsoft Exchange Server is a good example here. In this attack, the hackers sent arbitrary HTTP requests and authenticated as the Exchange server. Further, they could amplify the attack by gaining access to the OS and pivoting it to harm the entire organizational network. Broken user authentication and security misconfiguration were the reasons behind this attack.
Healthy API security practices can help improve a company's reputation. When users know their data is safe, it establishes trust and ensures loyalty, leading to more conversions.
Uber became a data breach target in 2016 when data of its 57 million consumers and drivers were compromised. The brand initially paid around $100,000 to the people responsible to stay quiet. However, they faced severe reputational damage when the incident became public.
So far, the examples have taught us that bad authentication practices and security flaws caused most attacks. Other security challenges need to be addressed to develop mitigation strategies. Learning about these threats will improve your security strategy and integrate the proper defenses.
As an API is open on the web, anyone who sends overwhelming API requests within a fixed time can render it non-functional. Hence, rate limiting or a threshold on API requests from a single source in a fixed time is necessary. No rate limit can attract brute force or DoS attacks.
Impaired Authorization Function or broken function-level authorization is a vulnerability in which anyone can perform specific actions without authorization. Proper access control policies and authorization checks must be enforced to address the BFLA challenge.
An SQL injection can significantly damage a company's reputation. It is endorsed due to lousy parsing and incorrect validation of request data. Injection flaws allow a hacker to inject malicious code and commands without authorization.
Sometimes, APIs return more data than the required data to user requests. Robert Hammers, Founder of Hammers Law Firm, noticed: “That can be a challenge for law firms as some of this data can be sensitive, leading to a violation of data privacy. Therefore, it is crucial to implement the principle of least privilege (POLP) to display only the required data. Further data anonymization and pseudonymization techniques can also work.”
This security challenge arises when proper authentication mechanisms still need to be implemented. It leads to unauthorized access to personal or sensitive data by hackers. The Parler API hack of 2021 is a good example. Hackers scrapped data from Parler that had no authentication methods and security measures in place.
In the heat of competition, developers may create new or updated APIs without any detailed documentation. This rush may prevent them from understanding how previous versions were implemented, leading to loopholes for hackers to harness.
The digital landscape constantly evolves with technological advancements, which leads to different security challenges. Your business needs to stay updated and vigilant in the face of these ever-changing digital threats.
While we have a rough idea of mitigating API risks, here are some best practices to strengthen API security:
The first thing you can do to ensure API security is to use SSL/TLS protocols. These protocols ensure data encryption between the API and the users while in transit - websites with HTTPS instead of HTTP in their URL employ SSL/TLS protocols.

To maximize security, your tools and applications must integrate the latest and most secure version of HTTPS and verify whether they are using the TLS 1.3 protocol.
Access or role-based access control is a scenario where specific users can access particular functionalities and data. For example, businesses that allow their users to access their data via an API should establish permissions and roles for access.
An administrator should be given full access, while an end-user should have limited access. The Zero-trust security model is an excellent model to use here.
Ensure that your APIs are kept behind a firewall or API gateway. To provide baseline protection, they should only be accessed through a secure protocol like HTTPS. This includes scanning for injection-based attacks and signature-based threats.
An API gateway is like a gatekeeper that acts as a shield between the API and the backend systems. It blocks unnecessary and malicious requests before they harm the backend systems. An active API gateway can help detect and defeat SQL Injection, Denial of Service, and Cross-site scripting attacks.
A good API gateway helps detect any vulnerabilities in your network that you might miss and increases security throughout your API landscape, reducing the chances of a security incident. What you need to do is to pick an API gateway with advanced filtering capabilities.
Authentication helps ensure that the user trying to access the API is legitimate. To ensure this, you can require secure ID/password logins to verify user identity before accessing your API. Using tokens, only users whose unique keys are already stored in the database will be granted access to the system.
Another way to prevent unauthorized access is to integrate multi-factor and biometric authentication. To add an extra layer of protection, you can also consider authentication protocols like OAuth 2.0, OpenID Connect, or SAML.
Authorization ensures that only authenticated users can access specific data or functionality. You can use POLP or the least privileged policy to prevent malicious users from accessing resources. The best thing about authentication and authorization is that they secure users from unauthorized access.
Implementing robust logging and monitoring activity is crucial. Regular audit logs can indicate how the users use the information and what they are accessing. Moreover, user activity logs can help you ensure compliance.
Conversely, real-time user activity monitoring can help track malicious activity, such as multiple failed login attempts or potential data security breaches. Auditing and logging help support the integrity and security, especially for SEO API. Ensure you have a clear logging and monitoring policy, and update it regularly to stay on top of the latest security risks.
Hackers who conduct SQL injection attacks tend to fabricate the inputs. Many attacks succeed due to poorly validated inputs. Hence, the input must be validated and cleaned before being fed to the API.
Ensure that all inputs adhere to the expected format. Specific tools and libraries like Postman and 42Crunch can help ensure the input's right type, format, length, and range.
Access to sensitive data, such as user financials, health records, trade secrets, medical records, PII, etc., should be restricted. Authorization policies or data encryption before transmission can help to protect data from potential misuse.
Consider different ways to control who can access your data, such as permission rules, encoding, tokenization, etc. Integrating e-signatures helps companies verify a user’s identity before accessing significant files. This option also improves document security by notifying when data is tampered with and tracking changes.
Timely security audits help identify and address API vulnerabilities before they are leveraged. You can collaborate with third-party websites to run external security audits to strengthen API security. You can also conduct internal audits and external evaluations. However, remember to amp up your internal security practices.
Security teams should regularly check the security controls protecting live APIs to ensure they function as expected and behave as documented. In addition to thoroughly testing APIs during development, regularly verifying the security controls for live APIs is essential.
With the advent of generative AI for test automation, testing APIs has become faster and more streamlined, allowing teams to identify and address vulnerabilities quickly. Update your APIs regularly with the latest security patches, new features, and bug fixes. That helps prevent attackers from exploiting known vulnerabilities.
Security is all about what kind of traffic you are welcoming. However, as it can be pretty comprehensive, it is best to implement robust security measures to ensure authenticity.
Cyberattacks can be catastrophic for a business in terms of money and reputation. Therefore, API security is the place to invest if you want to improve your customer experience and authoritatively maintain your market reputation. Implement the methods and ace the market.